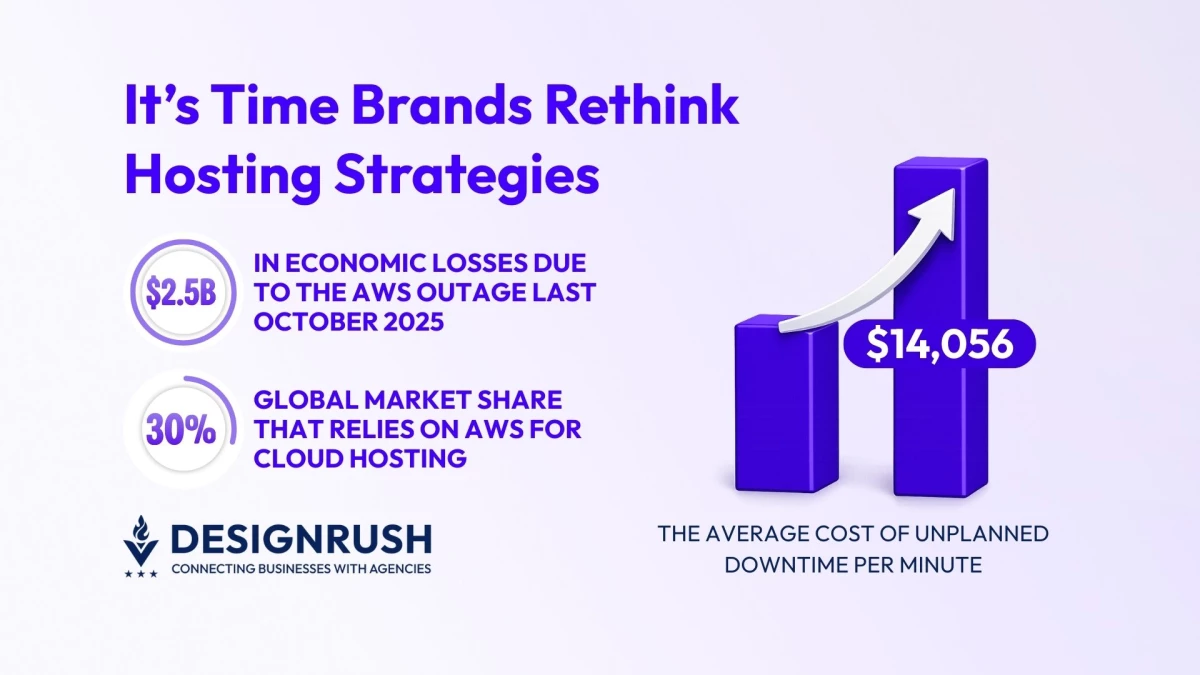
Multi-Hosting Strategy: Key Findings
- The AWS outage caused an estimated $2.5 billion in economic losses, showing how cloud disruptions now carry market-wide consequences.
- Unplanned outages cost businesses an average of $14,056 per minute, turning brief downtime into immediate revenue damage.
- Multi-host and automated failover setups reduce downtime exposure, making resilience a business requirement, not a technical luxury.
Back on October 20, 2025, some of the world’s most familiar digital services, from Alexa to Fortnite, went quiet for a few uncomfortable hours.
The culprit?
A DNS issue affected Amazon Web Services (AWS), one of the world’s leading cloud hosting services, causing communication errors between apps and their databases, websites and their login systems.
Experts estimate the outage cost everyone involved roughly $2.5 billion.
This outage was resolved quickly, but those hours of downtime clearly exposed how one small error could bring websites and apps to a screeching halt.
Naturally, such a moment impacts more than just the consumers who use these websites and apps.
AWS roughly owns 30% of the global cloud market, from startups to international corporations and everything in between.
For these companies, even just a few minutes of downtime can be costly.
A 2024 EMA Research study cited in a BigPanda report found that unplanned outages can cost companies nearly $14,056 per minute per incident.
For businesses operating at volume, even short disruptions translate into real revenue loss, customer frustration, and contractual penalties.
And as cloud adoption accelerates across industries, software and app developers like Empat warn of the risks of relying too heavily on a single backbone.
“The AWS outage of 2025 is the biggest proof that resilient hosting architecture is no longer optional,” said Dmytro Naumenko, Chief Business Development Officer at Empat.
“Brands simply cannot rely on one host for core channels anymore, unless they’re willing to experience how fragile revenue pipelines and customer trust can be in the face of an outage.”
Why Single-Host Dependency Creates Systemic Risk
Centralizing systems is a common practice because it offers speed and efficiency.
Unfortunately, centralization also concentrates failure.
“Relying on a single hosting provider creates a false sense of security,” said Naumenko.
“It simplifies operations on the surface, but underneath it concentrates risk in ways that only become visible during failure.”
Some of these hidden risks include:
1. Hidden coupling
Many organizations do not realize how much of their tech stack shares the same underlying infrastructure.
Authentication services, payment processors, analytics tools, and third-party APIs often sit on identical cloud foundations.
When that foundation falters, multiple systems fail together instead of independently.
2. Operational blind spots
Cost optimization and deployment speed tend to drive infrastructure decisions.
Failure scenarios rarely receive the same level of attention.
Teams design for growth and performance, then discover during an outage that redundancy was an afterthought.
Taken together, these weaknesses reveal why single-host dependency is not just a technical shortcut, but a structural liability.
Design Resilient Hosting Architectures
Resilience shouldn’t be a feature that gets toggled on at the end of deployment.
It is an architectural discipline that shapes how systems behave when things go wrong.
According to Empat, brands and development teams should adopt several strategies to ensure the resilience of their products.
1. Implement multi-host and hybrid deployments
True multi-host resilience starts with identifying which workloads actually need geographic and vendor diversity.
Core services like authentication, checkout, and customer data APIs should be deployed across at least two providers or paired with a cloud-plus-on-prem fallback.
Traffic routing tools and DNS-level load balancing can then be used to direct users to the healthiest environment in real time.
2. Build automated failover systems
Failover works best when it is boring and invisible.
Health checks should continuously monitor service availability, latency, and error rates.
When thresholds are crossed, traffic should automatically reroute to standby environments without waiting for manual intervention.
3. Separate critical services
Not all systems deserve equal treatment.
Payment processing, identity management, and core APIs should be isolated into separate failure domains so an outage does not block customer logins.
This segmentation limits the “blast radius” of an outage and preserves essential business functions.
Act Before the Next Outage Hits
The AWS outage should be treated less as a one-time fluke and more as a warning shot.
With the world becoming so reliant on digital infrastructure, reliability is now a glaring competitive differentiator.
Customers notice when services disappear. Regulators pay attention when disruptions affect critical operations. Competitors benefit when reliability gaps create openings.
However, the practical response is straightforward.
Leaders should audit dependency chains, map which systems truly cannot fail, and prioritize resilience upgrades before disruption forces rushed fixes.