The rapid advancement of AI brings both opportunities and challenges for brands and agencies. As they leverage AI for growth, they will inevitably encounter new cybersecurity threats, including from within.
This is why every business using AI should implement an Acceptable Use Policy for their employees.
Without proper employee training and clear guidelines on what is and isn’t acceptable, companies are likely to face significant issues, says Cheaper Than A Geek CEO and founder Christopher Barber.
Who Is Christopher Barber?
Christopher is the proudly proclaimed Chief Nerd at Cheaper Than A Geek, an IT services firm that specializes in helping small businesses with outsourced IT support. He has a strong background in creating customer-centric IT solutions and ensuring robust security measures for businesses. Christopher is dedicated to helping clients navigate digital threats with a focus on exceptional service and rapid incident resolution.
A long time ago Christopher built a computer, but when it failed to start, he had a terrible experience at a repair shop. Treated poorly and overcharged, he realized the need for an IT company focused on excellent customer service.
As an agency that was born out of a commitment to revolutionize the IT services industry by prioritizing exceptional customer experience, I was curious to hear what specific practices they employ to ensure customer service is always at the forefront of their operations.
“Oh goodness, a million things! But some of the most critical things start with our teammates. We hire talented technicians who speak English, not just nerds. At the end of the day, we are the liaisons between human beings and technology.
We also place a high priority on phone calls being answered by a live human being in an average of 18 seconds, and regularly conduct surveys to make sure we are 'hitting the mark'. Then lots of smaller things in between to make sure we have happy clients," Christopher explains.
When it comes to excellent customer experience, he suggests that conveying trust is important as the company manages critical aspects of clients' businesses and protects key data.
He says they hire less than 1% of applicants after thorough background checks. Additionally, he notes that their reputation also matters, and they guarantee complete satisfaction with their services.
Watch our video to discover the challenges and privacy concerns AI brings to businesses.
How to Avoid Internal AI Cybersecurity Risks
Discussing that cybersecurity has never been as important as it is today, especially with the rapid advancements in artificial intelligence, Christopher affirmed that AI affects different businesses in different ways.
“It is very important for every business to have an AI Acceptable Use Policy. If you don’t make it clear what is and isn’t acceptable, you are virtually guaranteed to have problems,” he advises.
By implementing a comprehensive AI Acceptable Use Policy, brands can proactively mitigate risks and ensure their cybersecurity measures keep pace with technological advancements.
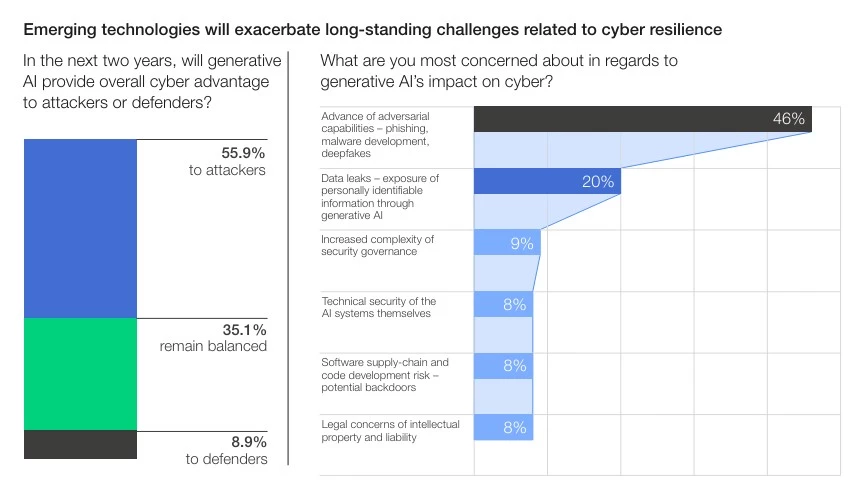
A survey among cybersecurity leaders suggests that 46% of them are most concerned about the advance of adversarial capabilities like phishing, malware development, and deepfakes in terms of the risks artificial intelligence poses for cybersecurity in the future.
Christopher notes that even with the best security measures in place, a business can still be compromised if an employee falls victim to a clever social engineering attack. Therefore, training and raising awareness among employees are vital for maintaining security.
That's where a professional IT team can help businesses handle this issue. Cheaper than a Geek does short video-based training and certifications for its client’s staff as well as simulated phishing attacks with corresponding reporting to ensure a safe environment, he explains.
Given the increasing threat of deepfakes, Christopher also advises businesses to protect themselves by verifying everything thoroughly, emphasizing to never trust information at face value.
For instance, if someone receives instructions to transfer money, they should make an outbound call to the client to confirm all transaction details, he advises.
Safeguard Your Data, Even in a Remote Environment
Many companies have shifted to remote work in the past years, mostly using cloud services to allow ease of access and teamwork. That, however, can make companies more exposed to cyber-attacks.
"We have always placed a high value on securing our clients at the endpoint level. So working from home was a natural fit for us. In addition to the typical endpoint security, we add EDR and network security (and sometimes content filtering and productivity monitoring) to ensure not just security but also productivity."
Christopher and I also touched upon Cheaper Than A Geek’s timeframe for resolving cybersecurity incidents.
He says that the company handles incident responses for clients experiencing security breaches quickly. According to him, in today's environment, acting quickly is essential; otherwise, the consequences could be severe.
“Different incidents require different responses and remediations, but inside of one week, having all said and done is our preference when possible,” he adds.
If you need assistance protecting your business from internal and external threats, our list of top cybersecurity companies is a great place to start.
Next, we touched upon common misconceptions about cybersecurity and I was curious to hear Christopher's opinion on the most prevalent misunderstandings businesses have regarding their security practices and measures.
This is what he told me:
“My favorite is 'Oh we are fine, our files (email, etc) are in the cloud'. I think most non-IT folks don’t realize the cloud is just a computer somewhere else. And that they’ve agreed to an End User License Agreement that disclaims any data or breach protection. You have to protect your data regardless of where it lives.”
Looking into the future, he also shared with me the biggest security risk that he believes we can expect in the next decade as technology continues to evolve
“At this point, it looks like AI-assisted cyber attacks could do some damage. The more realistic the attack, the more likely it is to succeed. Good cyber hygiene, combined with training and testing is key.”






