GDPR Compliance in Customer Support: Key Findings
- $1.4 billion in GDPR fines and $2.8 billion globally show customer support is a real financial risk, requiring brands to vet outsourcing partners beyond sales claims.
- Most failures stem from poor vendor choices, excessive access, and weak training, leaving little visibility into how data is handled.
- Strong compliance depends on tight access control, audit trails, and region-specific handling, ensuring clarity over who accessed data and why.
A Forrester Research report showed that approx $2.8 billion in privacy penalties were recorded globally.
DLA Piperalso reported that European regulators issued fines totaling more than $1.4 billion under the GDPR in 2025.
The moment a support team touches a European customer’s record, GDPR applies, regardless of where that team sits.
That enforcement picture matters for companies outside Europe because the risk follows the customer data, not the company address.
Hugo Inc., an outsourcing partner that designs and runs operational teams for healthcare and other high-complexity industries, says compliance in one jurisdiction may differ from that in another.
This becomes more complicated as support operations scale.
“Customer support is a key GDPR risk, which comes down to how teams actually handle data,” said Olufemi Onabowale, Global Head of IT and Information Security at Hugo.
“The risk doesn’t announce itself. It builds quietly inside decisions organizations make long before a single support ticket opens.”
Customer Support as a Data Access Point
Agents handle personal information, payment details, account credentials, and, in regulated industries, financial and medical records.
This makes outsourcing a governance issue, not just an operating choice, because customer support teams serve as a frontline access point to sensitive customer information.
According to Onabowale, “Data should be encrypted both at rest and in transit across every environment within support operations.
“Whether an agent is working from a delivery site or remotely operating within a client's cloud-based CX platform.”
That framework for outsourced support shows encryption only works as part of a broader control set that includes:
- Threat monitoring
- Multi-factor authentication with Single Sign-On (SSO)
- Role-based access
- Centralized permission management
- Background screening and training of support personnel
“Hugo operates primarily as a data processor,” Onabowale said, “because under GDPR, the client sets the purpose and scope of data use, while our support teams carry out the work within those boundaries.”
“Our Security and Compliance operations focus on ensuring the confidentiality and integrity of sensitive data through our integrated controls framework based on industry standards and regulatory requirements such as ISO27001, SOC 2, HITRUST, PCI-DSS, and GDPR.”
When regulators ask how a team handles sensitive data, an audit trail is the kind of information organizations would expect from any outsourced support partner handling regulated data.
Every interaction logged should capture the full lifecycle of a customer’s interaction and show relevant information about:
- Who accessed the data
- When access happened
- What actions were taken
- How records changed
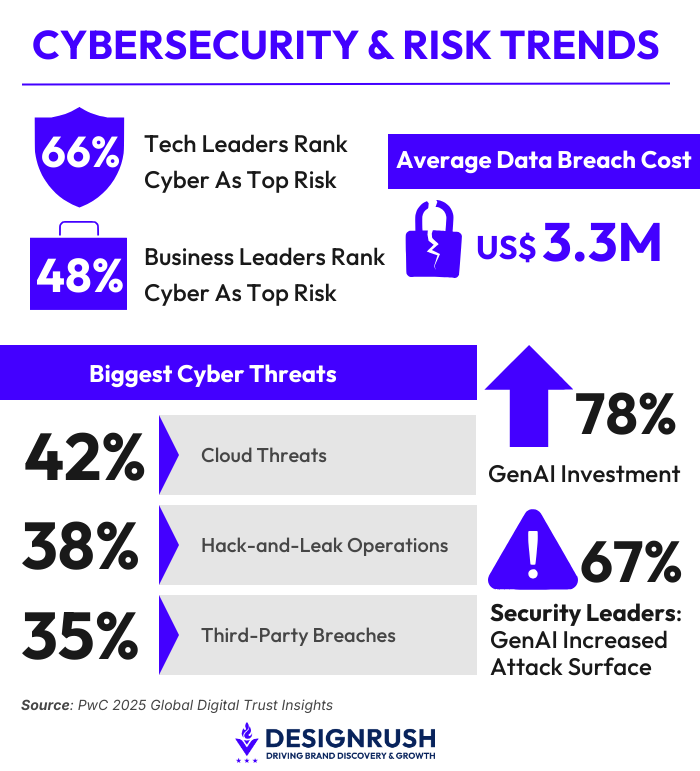
PwC’s 2025 Global Digital Trust Insights survey put the average cost of a data breach at $3.3 million and found that 35% of leaders ranked third-party breaches among their top cyber threats.
These numbers and the financial stakes make the case plain.
Where Support Outsourcing Becomes a Compliance Risk for Brands and Agencies
Breakdowns in outsourced support environments stem from operational decisions in how vendors are selected, how access is granted, and how teams are trained. This also includes:
- Choosing providers based on cost without checking controls
- Giving agents broader access than their tasks require
- Losing visibility across disconnected tools
- Underinvesting in training for teams handling customer data
“Customer data is most at risk at points of transition where context and permissions can break down,” Onabowale added.
Those points sit in everyday operations from data capture to internal handoffs and movement across platforms.
DLA Piper also highlighted that cross-border data transfers carry serious legal consequences in its review of the biggest GDPR fines in 2025, reinforcing how small operational gaps can translate into regulatory exposure.
This creates a practical set of requirements before any workflow goes live.
- Agent screening and training, including mandatory pre-employment background checks and onboarding in security and privacy protocols before workflow assignment.
- Clearly defined access rules, covering how data is collected, how it moves between agents, and how it is recorded across systems.
- Role-based permissions limited by task, not account-level exposure.
- Audit trails that capture who accessed customer data, when it happened, and what changed.
- Ongoing Monitoring and Reporting, including periodic internal audits in line with contractual, regulatory, and industry requirements.
What matters is not the presence of controls, but whether they hold up across every interaction involving customer data.
Security and compliance failures can only happen when controls fail under real operational pressure.
Adherence to recognized security hygiene practices such as the CIS (Center for Internet Security) controls, ISO 27001, NIST CSF (Cybersecurity Framework), etc., establishes the acceptable baseline for maintaining consistency and operational integrity across distributed support environments.
Regulators look at what happens with data in real operations, not how neatly it’s described in policy documents.
Most exposure sits in day-to-day support work, where access can stretch further than needed, and information passes through multiple hands without full visibility.
Even with outsourcing in place, the responsibility remains with the brand.
As such, the real test is whether controls still hold when activity increases, and errors become more likely.