The Big Leak Takeaways:
- A historic 16 billion credentials have been exposed, with major tech firms like Apple, Facebook, and Google among those affected.
- Researchers warn that fresh, weaponizable data opens doors for phishing, account takeovers, and wider cybercrime.
- Businesses are urged to adopt zero-trust models and better cybersecurity protocols to prevent crisis-level breaches.
It’s being called the biggest password leak in history for good reason.
Cybernews researchers have confirmed that an unprecedented 16 billion login credentials have been exposed, impacting some of the world's largest technology companies including Apple, Facebook, and Google.
"This is not just a leak — it’s a blueprint for mass exploitation," the Cybernews research team stated.
🚨 BREAKING: 16 BILLION PASSWORDS LEAKED: APPLE, GOOGLE, FACEBOOK USERS EXPOSED
— Mario Nawfal (@MarioNawfal) June 19, 2025
What’s being called the largest password leak in history has just been confirmed: 16 billion login credentials, many from major platforms like Apple, Google, Facebook, GitHub, and more, are now… pic.twitter.com/2Sxod46Hha
Unlike many past breaches that repurpose old data, Cybernews reports this one involves newly compromised information, collected across 30 massive datasets, some containing over 3.5 billion records each.
The exposed credentials cover a wide range of platforms, including:
- Social media accounts
- VPNs
- Developer portals
- Government services
The scale and freshness of the breach make it particularly dangerous.
Each dataset typically includes URLs, usernames, and passwords, which is everything a cybercriminal needs to launch widespread phishing attacks or gain unauthorized access to sensitive accounts.
Darren Guccione, CEO of privileged access management firm Keeper Security, chimed in on the matter.
He told Forbes that the passwords leak was a reminder of "just how easy it is for sensitive data to be unintentionally exposed online."
The dark web is already teeming with millions of stolen credentials available for purchase at shockingly low prices.
And the more comprehensive the dataset, the more valuable it becomes to malicious actors.
"The fact that the credentials in question are of high value for widely used services carries with it far-reaching implications," Guccione warned.
A Wake-Up Call for Preventive Action
The consequences of a data breach go far beyond reputational damage.
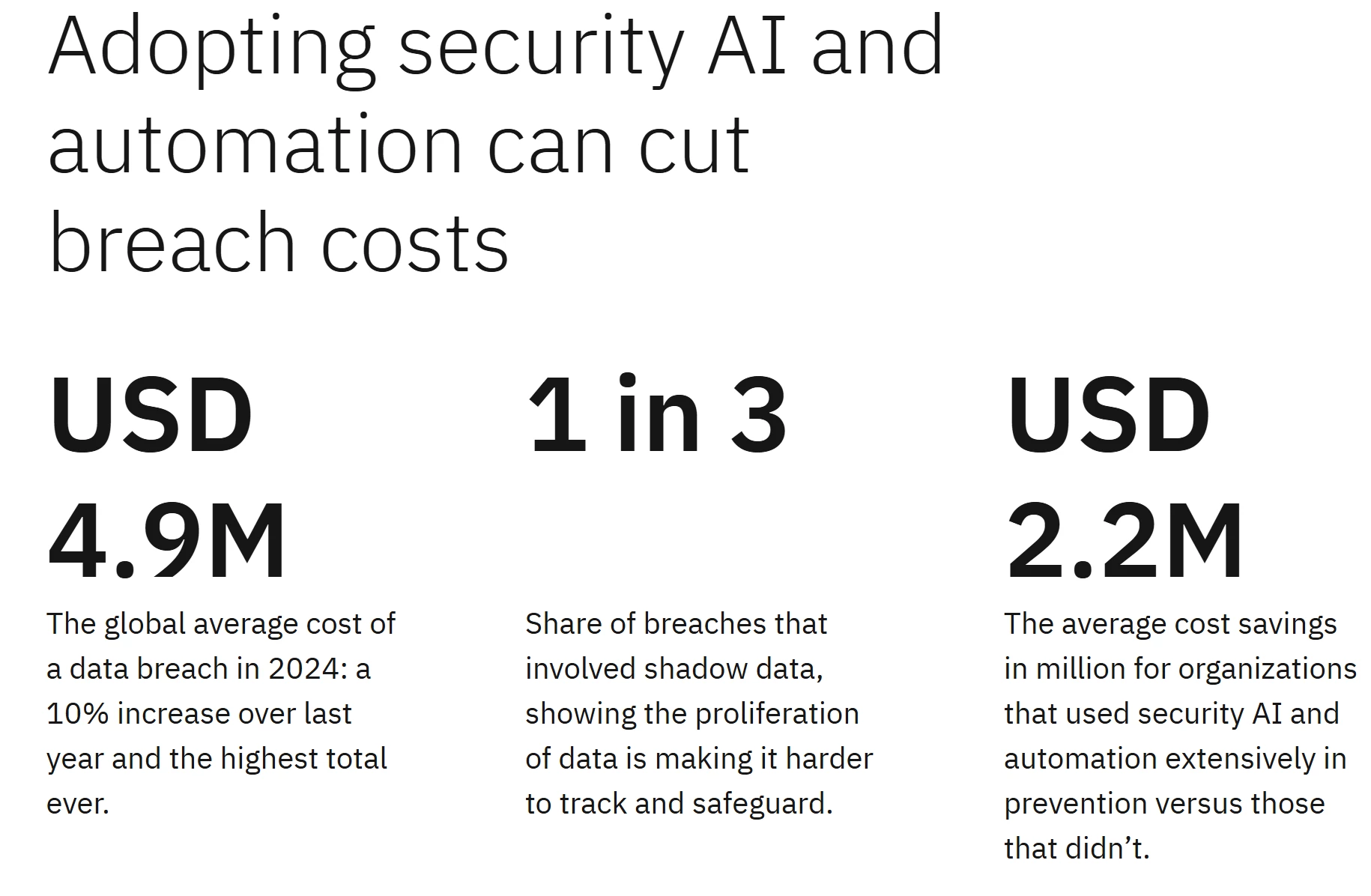
The average global breach now costs $4.88 million, according to IBM’s 2024 Cost of a Data Breach Report. This figure includes lost business, regulatory penalties, operational disruption, and the skyrocketing cost of incident response.
For businesses and consumers, the urgency to adopt stronger password management tools and dark web monitoring services has never been greater.
These tools can help alert users when their information surfaces on compromised lists, giving them a narrow window to take preventive action.
But businesses, particularly enterprises, bear a greater responsibility.
Guccione recommends that companies adopt zero-trust security models that enforce privileged access controls, ensuring that every access attempt is authenticated, authorized, and logged.
View this post on Instagram
"Organisations need to do their part in protecting users," added Javvad Malik, lead security awareness advocate at KnowBe4.
"People need to remain vigilant and mindful of any attempts to steal login credentials. Choose strong and unique passwords, and implement multi-factor authentication wherever possible."
How Businesses Can Stay Ahead
The scope of this leak isn’t just staggering — it’s a preview of what’s to come.
As cybercriminals grow more sophisticated and datasets become more expansive, companies can no longer afford to treat cybersecurity as a reactive function.
Organizations must adopt a forward-leaning approach that not only protects internal systems but also reassures customers that their trust is well-placed. This means shifting from passive defenses to active prevention.
Here are three essential cybersecurity strategies businesses should prioritize right now:
- Minimize Data Collection and Retention
Start by asking a simple question: Do we really need this data? Too many organizations collect and store vast amounts of personally identifiable information (PII) without a clear use case.
Instead, businesses should reduce what they collect, retain only what is essential, and set strict expiration timelines for data deletion. This minimizes the fallout if a breach occurs because there’s simply less to steal. - Implement Zero-Trust Security Models
The traditional castle-and-moat security model no longer works. A zero-trust framework assumes that no user, device, or system should be trusted by default, even if they’re inside the network.
Companies should enforce identity verification at every access point, adopt least-privilege access controls, and continuously monitor user behavior. This ensures that even if one set of credentials is compromised, the damage remains contained. - Audit and Limit Third-Party Access
Vendors, integrations, and SaaS platforms expand your ecosystem and your risk. Every additional partner introduces a new potential point of failure.
Conduct regular security audits of third-party tools, demand clear compliance documentation, and restrict access to only the data and services that are absolutely necessary. When possible, build on first-party infrastructure to retain more control and oversight.
Our Take: What Can Businesses Actually Learn from This?
For years, brands have encouraged consumers to hand over data in exchange for convenience and personalization.
But every breach like this forces people to question how much control they really have, and whether the tradeoff is still worth it.
For companies, the lesson isn’t just about patching vulnerabilities after the fact.
It’s about being far more intentional with the data they collect in the first place.
If information isn’t mission-critical, don’t store it. The less you keep, the smaller your exposure when something goes wrong.
This should also be a wake-up call to rethink over-reliance on third-party vendors.
Every integration adds another crack to the system. First-party data, built on direct relationships with customers, gives brands more control, more security, and ultimately, more trust.
And trust isn’t built through promises made after a crisis.
It’s earned through transparency long before anything goes wrong.
This is done by:
- Openly communicating policies
- Showing how data is protected
- Treating data privacy as a core brand value, not a legal obligation.
In the end, trust isn’t given but continually earned.
And in this environment, it’s one of the most valuable assets a brand can protect.
Earlier this year, Bybit experienced a massive cyberattack, where its ETH cold wallet was hacked for a whopping $1.46 billion.
See how top teams keep brands secure and trusted. Check out the best cybersecurity agencies:






