eCommerce Website Security: Key Findings
- Adobe’s October 2025 Magento security patch was released last October 14, fixing the critical CVE-2025-54236 REST API flaw.
- Magento powers 10% of all U.S. and 18% of all European eCommerce websites, meaning vulnerabilities on the platform can have global consequences.
- Global B2B eCommerce is expected to hit $36 trillion by 2026, underscoring why cybersecurity discipline will define success.
Adobe has just played a countermove in its never-ending chess match against opportunistic, malicious cyberattackers.
Adobe released a critical 2.4.8-p3 security patch for Magento and Adobe Commerce last October 14, 2025.
The new update addressed several high-priority vulnerabilities that could allow unauthorized access and data exposure directly through the platform’s core architecture.
The vulnerability, named CVE-2025-54236, affects REST API endpoints and could be exploited through chained attacks that target authentication gaps and logic flaws in the Magento framework.
All brands using Magento and Adobe Commerce are highly advised to update to the latest patch.
The fixes Adobe has implemented are as timely as they are vital.
According to Statista, Magento is the fourth most-used platform in the U.S, with a market share of 10%.
Meanwhile, the platform is the most popular eCommerce platform in Europe (tied with WooCommerce), with a market share of 18%.
This widespread adoption makes every vulnerability a significant threat to both brands and their customers.
Likewise, it marks a growing problem affecting many SaaS solutions: the accelerating pace of patch releases.
Yet, enterprise eCommerce experts and agencies like Bighorn Web Solutions warn that frequent security patches aren’t a particularly efficient and secure solution:
“Security patches are essential, but relying on them alone is like playing perpetual catch-up. True protection comes from proactive monitoring, regular audits, and embedding cybersecurity best practices into every layer of your eCommerce infrastructure,” said Caleb Bradley, Founder and CEO of Bighorn Web Solutions.
In other words, keeping your eCommerce business secure requires a shift in mindset and an investment in the right security systems and processes.
Why Patching Alone Isn’t Enough
Security patches are similar to closing an open door. It’ll stop someone from strolling in, but it’s still not secure as it isn’t locked.
Despite this, many merchants mistakenly believe that applying updates is enough to guarantee safety.
The truth is that patches are only one layer of defense. Just as a bank has security personnel, CCTV systems, vaults, and the like, eCommerce websites should have several security measures in place.
This is because even when Magento itself is up-to-date, unpatched third-party extensions, like payment gateways or shipping calculators, or even the design of a website can reintroduce old risks.
Other common pitfalls include:
- Staging errors: Deploying patches directly to production without proper testing
- Version mismatches: Extensions and plugins that conflict with the latest build
- Neglected environments: Unpatched development or backup websites
Take Ownership of Your Security
Protecting an eCommerce site requires structure, not improvisation.
This means merchants need to have a clear cybersecurity plan in place to adequately evaluate, apply, and maintain security without breaking site performance.
To do this, Bighorn Web Solutions offers the following steps:
1. Audit and Update Extensions Regularly
Unmaintained extensions are one of the most common points of entry exploited by cyberattacks.
As such, merchants should schedule a regular review of all third-party Magento extensions for version compatibility and security support. This should be done no less than once a quarter.
If any redundant or outdated plugins are found, these should be replaced immediately to avoid introducing conflicts with the latest version of Magento
This proactive review also keeps performance optimized and codebases cleaner.
2. Harden Access and Authentication
Weak credentials and unrestricted access are like staging an open house for hackers.
Merchants should strengthen who can access admin panels and sensitive APIs to essential employees. Ideally, limit high-level access privileges to the least number of people possible.
Additionally, it’s advised to rotate and vault API keys and service credentials regularly.
Likewise, pair tighter access controls with runtime protections such as a web application firewall and anomaly detection that flags unusual login patterns or credential stuffing attempts.
All together, these measures can minimize the “blast radius” of a breach, as well as buy time for teams to deploy countermeasures effectively.
3. Establish Long-Term Compliance Practices
Businesses that stay secure and thrive on Magento do so because they tend to implement continuous monitoring tools.
These tools help document every patch cycle, maintain version control systems, and detect anomalies early.
Assign ownership of these tools to either an internal IT team or a trusted agency partner. This will keep the process consistent.
Protect Your Growth Driver
It’s no secret that an eCommerce website is a key growth driver for many businesses.
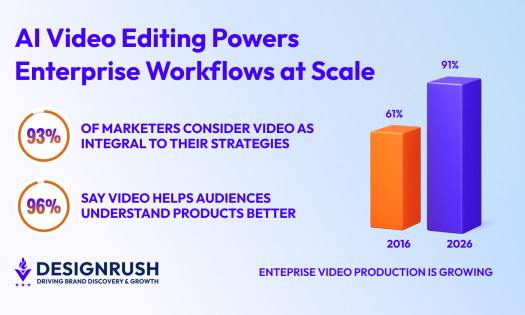
This is evidenced by the fact that the International Trade Administration expects the value of global B2B eCommerce to grow to $36 trillion by 2026.
As such, the most successful eCommerce brands won’t be the one that spends the most on ads. It’ll be the ones who can protect their main growth driver the best.